The risk of noncompliance does not increase linearly. Exceptions increase, and audits become more challenging as teams add regions, PSPs, partners, and internal roles. By emphasizing audit-ready operations – controlled access, governed by exceptions, and rapidly retrievable evidence trails – EAERA is intended to maintain compliance under expansion.
What “Long-Term Compliance” Means in 2026
A policy document is not a long-term compliance. It is the capacity to demonstrate that controls are implemented consistently over time, despite staff changes and volume increases. In 2026, partners and regulators evaluate the presence of controls as well as their dependability.
EAERA frames long-term compliance as operational consistency plus evidence. Most failures happen when operations depend on human memory and informal workarounds. The pattern is predictable: teams handle edge cases manually, logs become incomplete, and ownership becomes unclear.
Long-term compliance is defined by EAERA as operational consistency plus proof. When operations rely on human memory and unofficial workarounds, the majority of failures occur. EAERA is designed to prevent that by making compliance with system behavior.
Audit-Friendly Design: Evidence First, Not After-the-Fact
The fundamental premise of audit-friendly design is that you should never need to “reconstruct” a crucial event from spreadsheets and emails. As a natural byproduct of its operations, the platform ought to produce evidence.
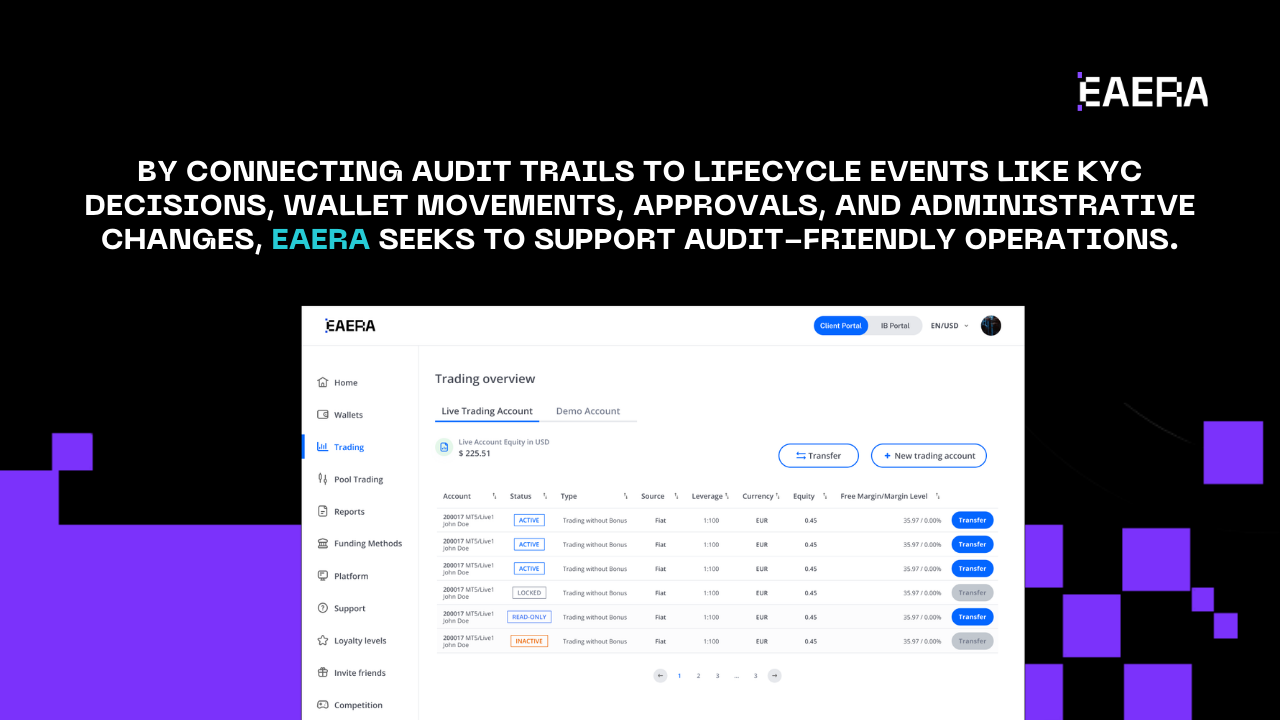
By connecting audit trails to lifecycle events like KYC decisions, wallet movements, approvals, and administrative changes, EAERA seeks to support audit-friendly operations. Transparency in data logging is important in this situation. Teams are forced to improvise when a system conceals operational history. A timeline-exposing system enables teams to demonstrate what is transpired.
“Who/what/when/why” is a useful method for assessing audit readiness. You should be able to see who carried out the sensitive action (or which system actor did it), what changed, when it occurred, and why.
Audit artifacts the platform should be able to produce:
- Client lifecycle timeline (registration, KYC submission, decisions, changes)
- Wallet event log (deposit/withdraw states, reversals, failures, confirmations)
- Approval trails for sensitive actions (submitted, reviewed, approved, executed)
- Policy or configuration change logs with effective dates
- Evidence exports for disputes (threshold, measured value, timestamp)
- Admin action history (who changed access, limits, or statuses)
Because audit readiness becomes essential as scale grows, EAERA places a strong emphasis on audit-friendly design. Your operational risk decreases with the speed at which you can obtain evidence.
Role-Based Access Control: Permissioning That Scales
Informal guidelines like “only finance handles withdrawals” become ineffective as the company expands. Boundaries must be enforced by the system. Compliance becomes feasible at scale through role-based access control.
Sensitive actions can be tracked and limited to the appropriate roles thanks to EAERA’s design, which is based on RBAC principles. This lessens inadvertent errors and clarifies accountability. Additionally, RBAC encourages separation of duties, which is crucial for partner modifications, KYC choices, and money transfers.
Focus on high-risk operations, such as payout approvals, wallet adjustments, KYC approvals, commission rule changes, and account permission updates, rather than listing permissions as a lengthy matrix. These actions are not “available to everyone who needs help” in a scale-ready system. They have permissions, and the modifications to those permissions are recorded.
Manual Override Logic Governance: Controlled Exceptions Without Chaos
Overrides are necessary for any true business. PSPs fail. False positives are flagged by KYC vendors. Edge-case documents are submitted by clients. Exceptions are a part of operational reality, and they require a controlled path.
Overrides are not a risk to compliance. Overrides that occur informally, without reason codes, without approvals, and without an evidence trail pose a risk. “One-time exceptions” become systemic gaps in this way.
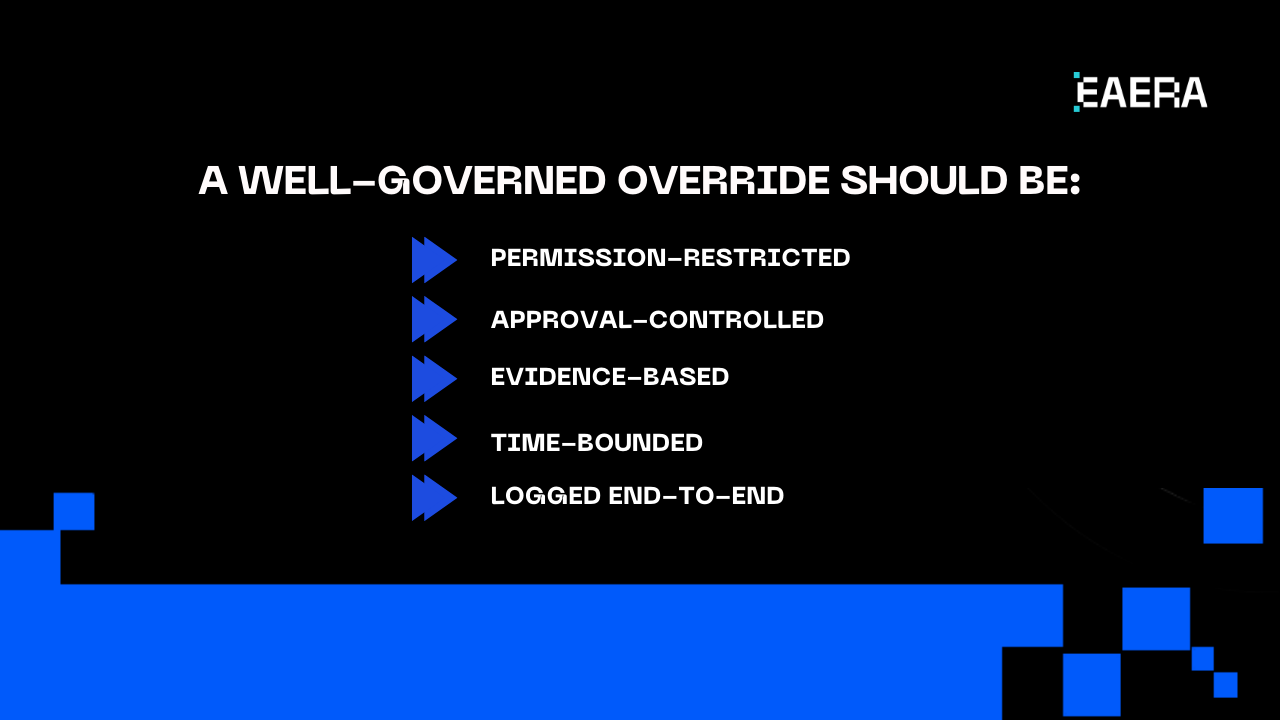
EAERA supports the concept of override governance by treating overrides as first-class events. A well-governed override should be:
- Permission-restricted (only specific roles can request or apply)
- Approval-controlled (maker-checker for high-risk overrides)
- Evidence-based (reason codes plus linked case context)
- Time-bounded (override expires or reverts automatically)
- Logged end-to-end (request, approval, application, removal)
This is important, as demonstrated by a straightforward scenario. Operations uses a different payout method when a withdrawal is held because of a PSP issue. In a governed system, the final action is traceable, the override request and approval are logged, and the initial hold is recorded. In this way, exceptions can still be justified in a subsequent audit.
KYC Integration Limitations: What Platforms Can’t Solve for You
One of the most misinterpreted aspects of fintech operations is KYC. Many businesses anticipate that a KYC integration will automatically generate clear “approve/deny” results. There are significant regional, document type, and risk policy differences among KYC providers. There are hard limits to even the best integrations.
KYC integration limitations you must plan for:
- False positives (legitimate clients flagged)
- Edge-case documents (regional formats, low-quality scans, mismatched scripts)
- Manual review requirements that cannot be eliminated
- Regulatory differences between jurisdictions
- Data quality and latency issues from vendors
These restrictions cannot be eliminated by software alone on a platform such as EAERA. It can make them manageable from an operational standpoint. That means queue-based handling, clear ownership and SLAs, consistent decision logging, and evidence capture for approvals and rejections.
“Late-stage KYC shock,” where verification only becomes a barrier during withdrawal, is the main compliance risk to avoid. Even when manual reviews are necessary, KYC timing must be made clear and consistently enforced for long-term compliance.
How to Validate EAERA Compliance Readiness
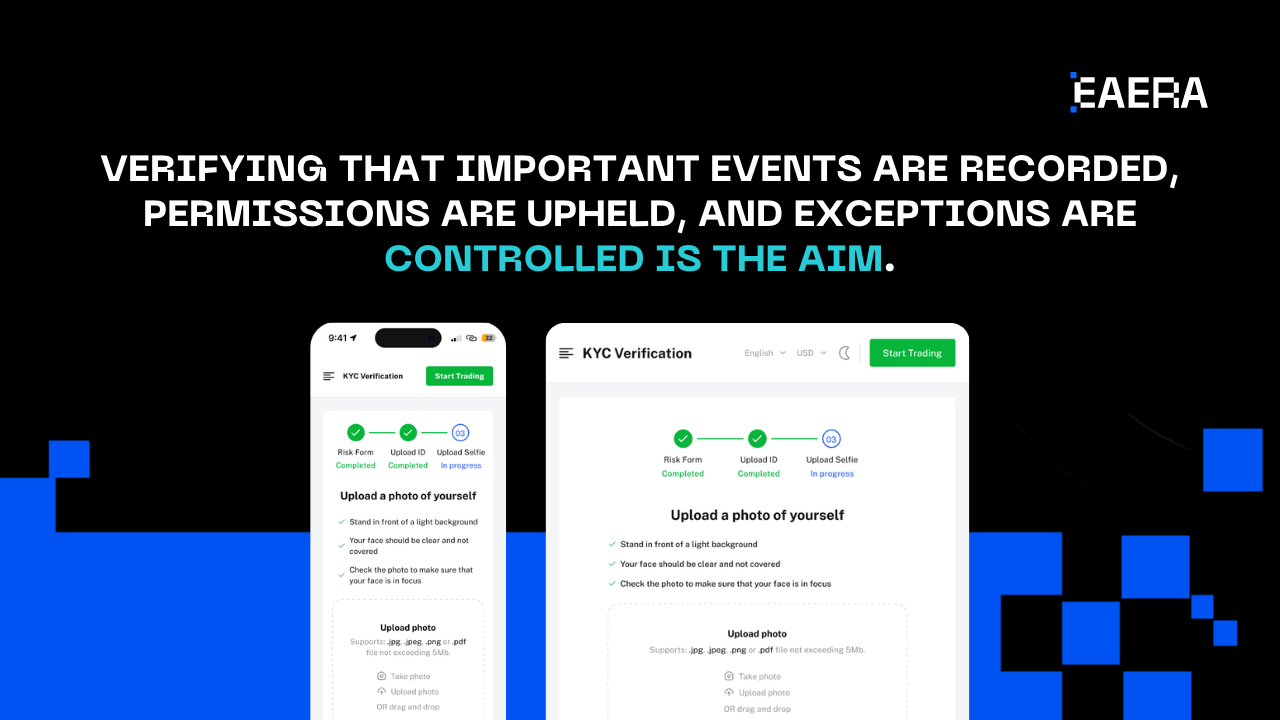
An end-to-end walkthrough in a demo or pilot is the most dependable validation technique. You want to demonstrate that EAERA enforces controls and generates evidence in actual workflows, not just in policy statements.
Creating a client, submitting KYC, processing a deposit, requesting a withdrawal, applying a controlled override, and exporting an audit report with the timeline and actors are all simple steps in a practical walkthrough. Verifying that important events are recorded, permissions are upheld, and exceptions are controlled is the aim.
The minimal requirements for scaling are straightforward: wallet events must form a comprehensive timeline, overrides must be auditable with reason codes, withdrawals and adjustments must have approval trails, and KYC decisions must be traceable with ownership. Scale will increase risk if those requirements are not consistently met.
Evidence combined with operational consistency constitutes long-term compliance. Through audit-friendly design, role-based access control, governed manual overrides, transparent data logging, and a practical approach to KYC integration limitations, EAERA is built for that reality. Verify it using actual workflow walkthroughs, then scale with assurance.